About VAULT
Deliver fast, frictionless onboarding and consistent connectivity across every store, venue, and location
VAULT enables passwordless, roaming that keeps visitors connected while maintaining enterprise-grade security and control.

The Visitor Experience
From entry to exit, connectivity simply works.
The moment a visitor enters your store, shopping center, or public venue, their device connects seamlessly using secure PSK authentication. As they move throughout the space, the network recognizes them and maintains uninterrupted access.
No captive portals (unless you’d like one). No repeated logins. No friction.
The result is a secure, consistent digital experience that supports every step of their visit — making onboarding effortless while keeping connectivity reliable across the entire environment.
Optional Captive Portal
VAULT automatically confirms the user’s identity and privileges then redirects to a unique welcome page once connected to Wi-Fi.
Serve coupons or ads based on the user’s previous spending behavior as soon as their device connects. Or get rid of the captive portal altogether and just let the user connect to the network.

With VAULT, Device Connections are PSK-based
Every device in the world supports PSK, and virtually every device owner knows how to use them.
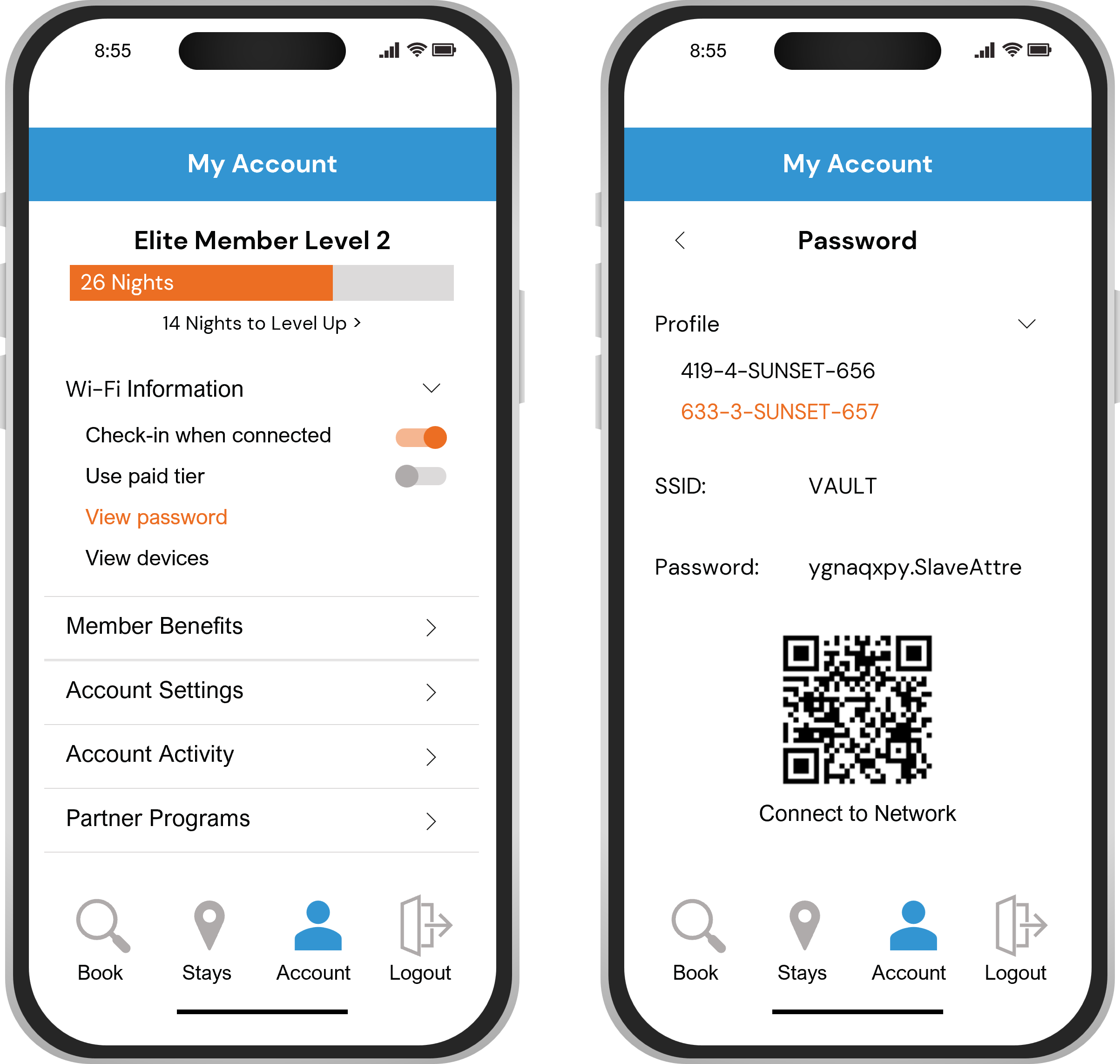
App Integration
Enhanced guest data with location-based services
Drive app downloads by providing passwords in the app